How Quantum Computing Will Transform Data Security in the Next Decade
Quantum computing uses qubits to solve complex problems exponentially faster than today’s computers. While this promises massive innovation, it also threatens to break the RSA encryption that currently secures our global financial, medical, and government data. To combat the "Harvest Now, Decrypt Later" threat, the tech world is shifting toward Post-Quantum Cryptography (PQC)—new mathematical defenses designed to be "quantum-proof." The next decade will be a race to upgrade our digital infrastructure before these powerful machines become a reality.
For decades, the security of our digital world has rested on a foundation of "hard" mathematical problems. Whether you are sending a private message, accessing your bank account, or securing state secrets, your data is likely protected by encryption that would take a classical supercomputer trillions of years to crack.
But we are approaching a transition point. Quantum computing, once a theoretical curiosity of physics labs, is rapidly becoming a reality. When these machines reach maturity, they won't just be faster than our current computers—they will be fundamentally different, capable of unraveling the very fabric of modern cybersecurity.
The Fundamental Shift: From Bits to Qubits
To understand the threat, we first have to understand the power. Traditional computers use bits—binary switches that are either 0 or 1. This is linear; to solve a complex puzzle, a classical computer essentially tries every key one by one until it fits.
Quantum computers use qubits. Thanks to the principles of superposition, a qubit can represent 0, 1, or both simultaneously. Furthermore, through entanglement, qubits can be linked so that the state of one instantly influences another, regardless of distance.
This allows a quantum computer to explore a vast landscape of possibilities all at once. For certain tasks, a quantum machine can find the "key" in seconds, whereas a classical computer would still be trying the first few million combinations.
The "Quantum Apocalypse": Why RSA is at Risk
Most of today’s encryption (specifically public-key cryptography like RSA) relies on the fact that it is incredibly difficult for a computer to find the prime factors of a very large number.
In 1994, mathematician Peter Shor developed Shor’s Algorithm. He proved that a sufficiently powerful quantum computer could factor these large numbers almost instantly. This means that the moment a "Cryptographically Relevant Quantum Computer" (CRQC) is switched on, the following become vulnerable:
Financial Transactions: Banking systems and credit card processing.
Government Communications: Classified data and diplomatic cables.
Blockchain and Crypto: The private keys securing digital assets.
Digital Signatures: The technology that verifies the software you download hasn't been tampered with.
While we don't have a CRQC yet, the threat is looming. Many experts predict we are only 10 to 15 years away from this "Quantum Day Zero."
"Harvest Now, Decrypt Later"
You might think, "If the computer doesn't exist yet, why should I care today?" The danger is a strategy known as Harvest Now, Decrypt Later (HNDL). Nation-states and sophisticated cybercriminals are currently intercepting and storing massive amounts of encrypted, high-value data. They cannot read it today, but they are betting that in a decade, they will have the quantum power to unlock it. If your data (like health records or trade secrets) needs to remain secret for more than ten years, it is already at risk.
The Defense: Post-Quantum Cryptography (PQC)
The good news is that the cybersecurity community is fighting back. We are currently in the midst of a global migration to Post-Quantum Cryptography (PQC). These are new encryption methods that rely on different types of math that even a quantum computer cannot easily solve.
1. Lattice-Based Cryptography
Instead of prime factoring, this method hides data inside complex, high-dimensional geometric structures called lattices. Finding a specific point in a thousand-dimensional lattice is a problem that remains "hard" for both classical and quantum machines.
2. Quantum Key Distribution (QKD)
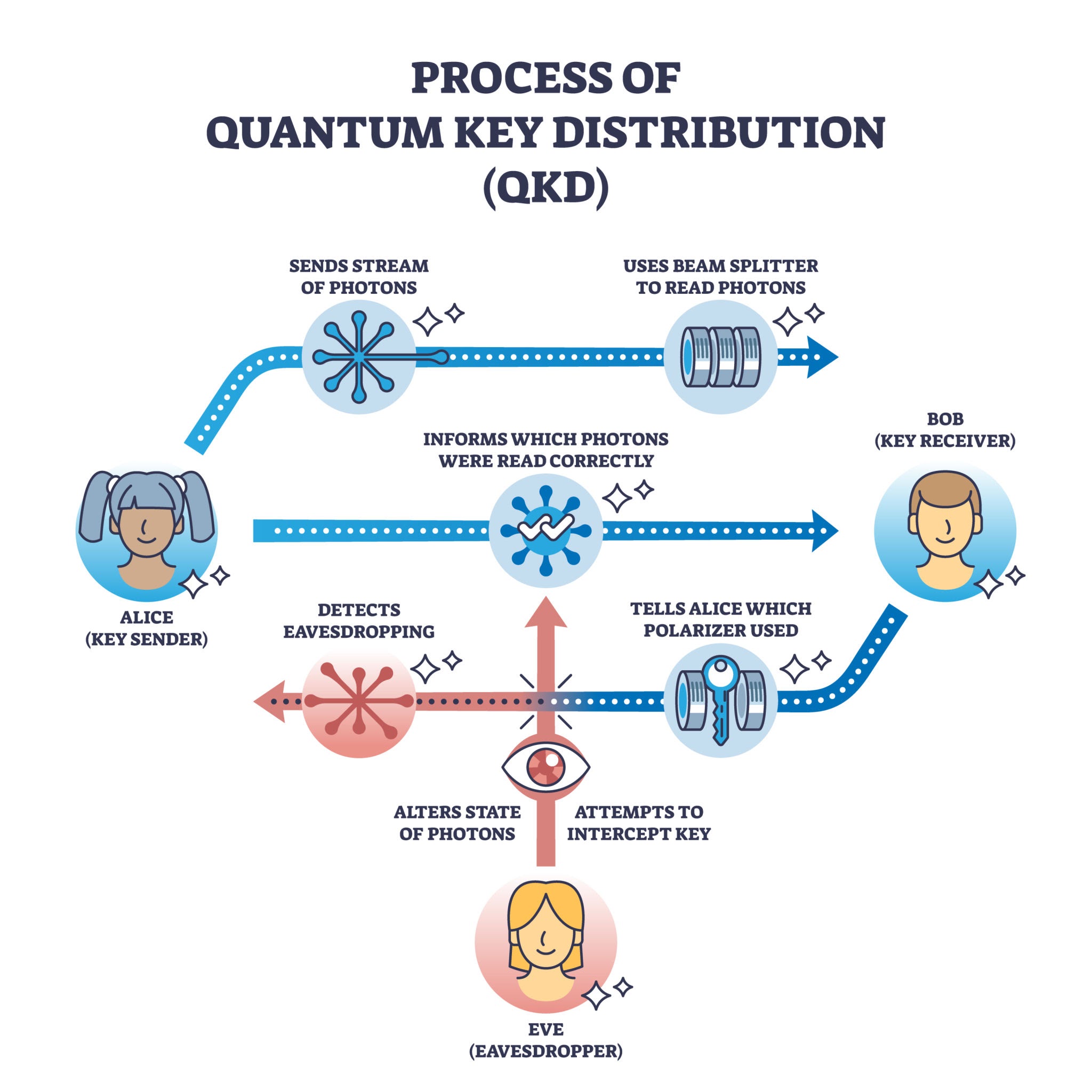
QKD uses the laws of physics rather than mathematics. It involves sending encryption keys using individual light particles (photons). According to the laws of quantum mechanics, the act of "observing" a quantum system changes it. If an eavesdropper tries to intercept the key, the photons are altered, the users are alerted, and the key is automatically discarded.
How Businesses Should Prepare
The transition to a quantum-secure world will be the largest migration in the history of computing—likely more complex than the Y2K bug. Here is how organizations are beginning to prepare:
Quantum Risk Assessment: Identifying which data is most vulnerable to "Harvest Now, Decrypt Later" attacks.
Crypto-Agility: Updating IT infrastructure so that encryption algorithms can be swapped out easily. Instead of hard-coding one type of security, systems are being built to be "agile" enough to adopt new NIST-standardized PQC algorithms as they arrive.
Hybrid Encryption: Many early adopters are using a "double-wrap" method—encrypting data with both current RSA/AES standards AND a new post-quantum algorithm. This ensures that even if one is compromised, the other remains standing.
Conclusion: A Decade of Transformation
The next ten years will be a race between the engineers building quantum computers and the mathematicians building quantum defenses. While the "Quantum Apocalypse" sounds like science fiction, the steps we take today—adopting PQC and building crypto-agile systems—will determine whether the quantum era is remembered as a security disaster or a new frontier of technological possibility.
